IT Consultancy
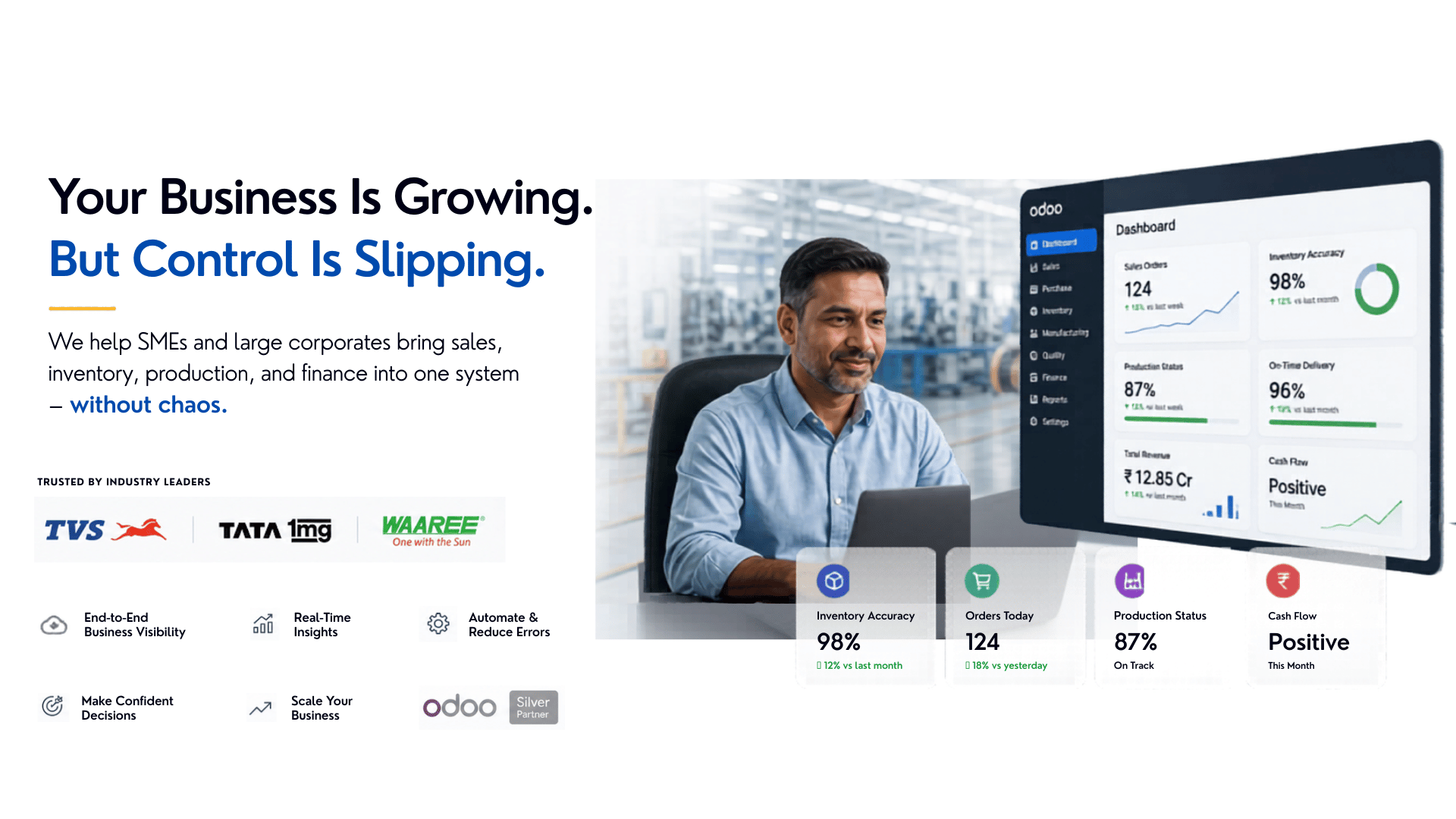
As a technology-driven organization, we take pride in offering expert advisory services on all aspects of IT strategy, infrastructure, and startup technology solutions. Leveraging Generative AI (GenAI) in the Software Development Lifecycle (SDLC), we enhance requirement analysis, code generation, testing automation, and deployment optimization, ensuring faster development cycles and higher software quality.
As your external IT partner, we integrate AI-powered automation and intelligent insights into your development process, enabling cost-effective, scalable, and innovative solutions. Our goal is to help you maximize the value of your technology investments by adopting cutting-edge AI capabilities, streamlining operations, and accelerating business growth in an increasingly digital landscape.
















Helping companies across the globe to onboard the technical talent via right hiring, staffing and training
Manju Aggarwal Director - Staffing